SpotMon
Identify & Prevent Salesforce Bad Actors
The AI-Powered Solution for Salesforce Shield Event Monitoring
.png?width=2000&height=1126&name=spotlight%20(5).png)
How SpotMon works
SpotMon is the fastest way to get up and running with Salesforce Shield Event Monitoring
1. Automatically generate tolerance levels
Tolerance levels are auto generated based on your company's user behavior.png?width=2000&height=940&name=spotlight%20(6).png)
.png?width=2000&height=1126&name=spotlight%20(5).png)
2. Monitor suspicious user activity
Get real-time alerts for highly unusual or suspicious activities
3. Investigate & take action
Pinpoint the exact nature of suspicious activities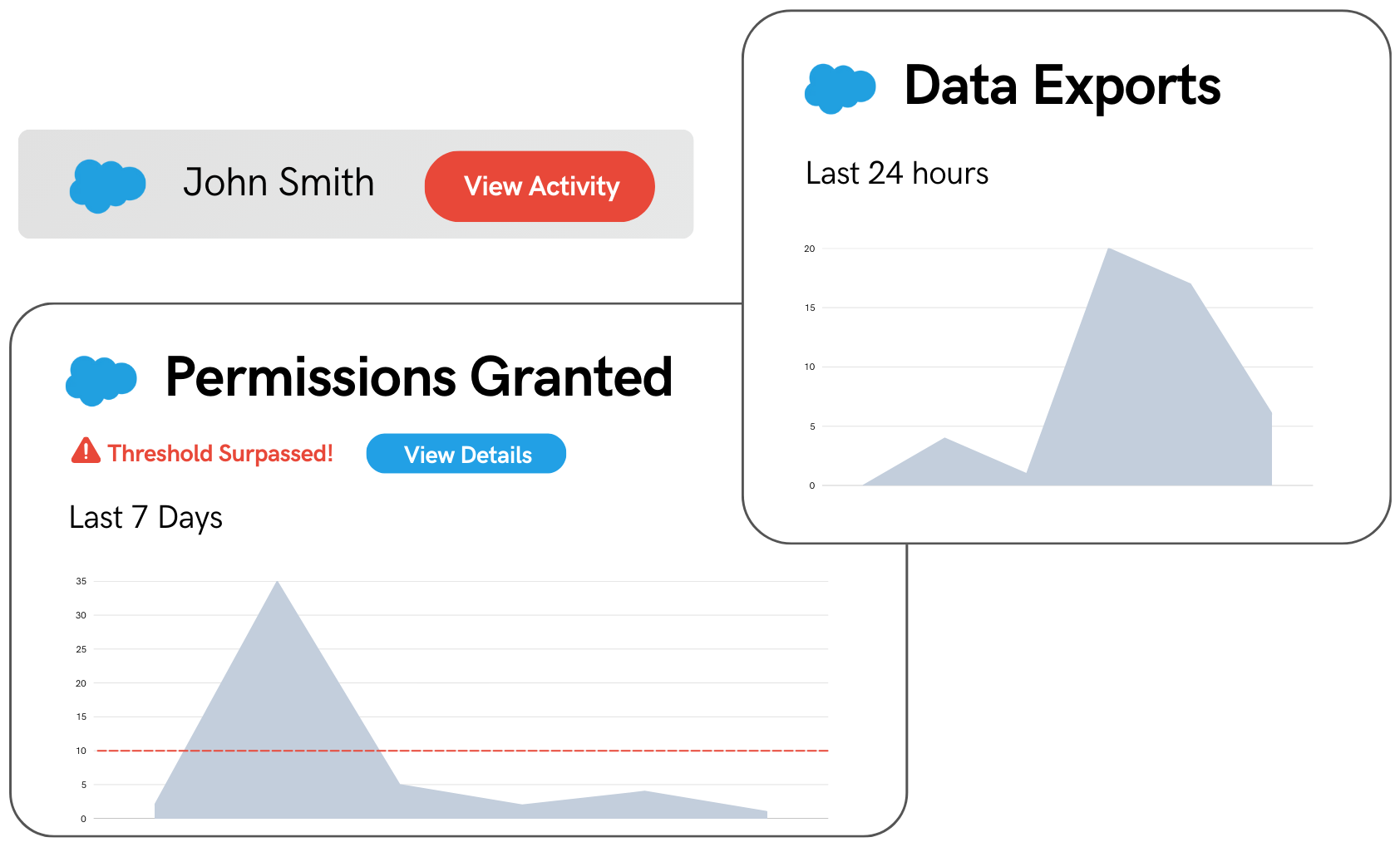
Key questions SpotMon answers for:
Why SpotMon
-
60% of data breaches are from internal users
-
SpotMon is a turnkey solution for Salesforce Event Monitoring and investigating Salesforce user activity
-
Built by Salesforce Shield experts
